Stolen Identity Prevention Tips That Everyone Needs To Know

One Case of Stolen Identity Can Seem Unimportant - Until It Happens To You
Stolen identity; the two words have a very dubious effect on those who hear it from others. It gives you a false impression of distance in that you know it happens, you know it can completely upend one's life, but you're relatively safe from the threat. Maybe its because there is no real threat of physical violence that makes people think that it can never happen to them or maybe you think you are safe because you're not rich, but you would be wrong. The real reason that identity theft is becoming more common is that criminals are catching on that your identity is what's valuable because of what it can give them - anonymity.
If you've never underwent the special torture that a stolen identity can give you, then count yourself lucky. Follow the suggestions in this lens and you may continue to enjoy your good luck, but if after reading it and discovering things you are not currently doing, you're pushing your luck if you don't make some changes. I hope you find this lens useful and it keeps you from ever having to experience this massive headache.
Photo by lydiashiningbrightly / flickr.
Stolen Identity Poll Question
Have you ever had your identity stolen or know someone who has?

Ways That Thieves Steal Your Identity
1-The outright stealing of credit cards, checks, passports, etc. is still very popular. It's wise to keep copies of numbers in a safety deposit box so you can cancel them easily. Would you know your passport information if it got stolen?
2-Guessing weak passwords.
3-Going through your trash. It's not even considered trespassing if they do it from the curb. Use a crosscut shredder or burn all documents with important numbers on them.
4-Using fake job offers to get people to send in resumes full of valuable information.
5-Hand-held credit card readers can be used from a distance and some can even read information while your card is still in your wallet or purse.
6-Public records can be a stepping stone for stolen identities, and there's not much we can do about that.
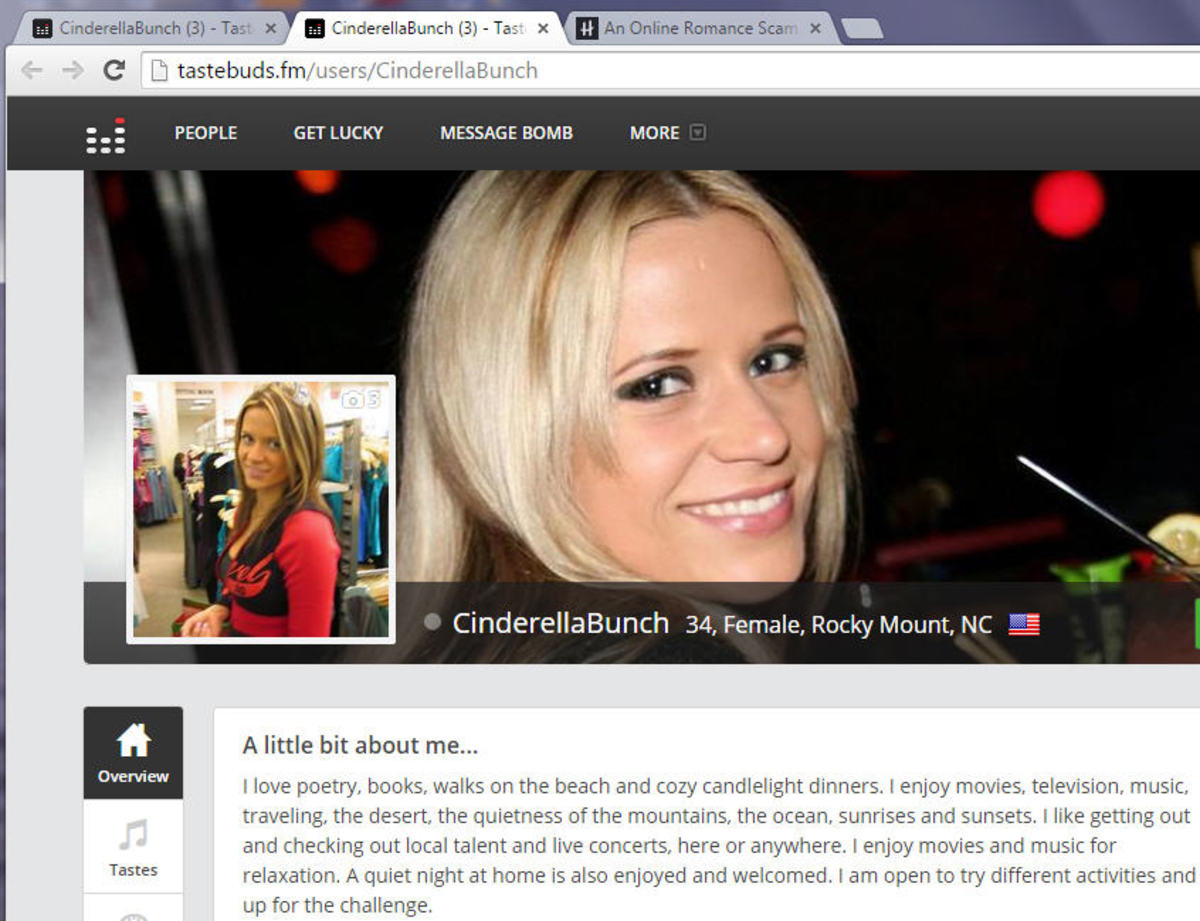
7-Looking on social network sites (facebook, etc.) for information they can use or befriending individuals until they get that information.
8-Getting jobs at legitimate companies that store and use information just to steal and exploit from them.
9-Information can be retrieved from old computers, memory sticks or mobile phones by some. The only way to guarantee that it doesn't is to completely destroy the memory cards.
10-Tricking individuals by phone to divulge useful information. Never give out such information if they call you; if you call them, that's another story.
11-Infecting your computer with spyware trojan viruses to get your passwords.
12-Having contests in which those entering have to put down valuable information.
13-High resolution pictures of yourself on the internet can be used to put on fake ID's.
14-Fake e-mails that look very legitimate. It's very easy to get exact copies of company logos; always call the contact number you have if not sure.
15-Looking over your shoulder why you type in your passwords at ATM machines.
Books About Stolen Identity

Stolen Identity Opportunity Case Study
What happens to all those losing contest entries?
My husband and I were walking through a local trail and picking up garbage, like we always do on our walks. We always find tell-tale evidence of what the folks who'd left the garbage were doing (beer cans, candy wrappers, etc.); the typical trash one would expect. Recently however, we found a plastic bag full of contest entries written on pieces of paper from a well known business franchise in town. I won't mention the name of the franchise because I don't want to do anyone harm, but I feel the public should be made aware that entering contests like these can be another way for their identity to be stolen. Each entry had the entrant's name, birthday, phone number, gender, signature and full address. There were probably 50 of these pieces of paper, with 50 different identities on them. There was nothing on the pieces of paper to say that the information provided would be protected or no indication that the information was safe in the company's possession. These people had unwittingly entered a contest to potentially have their contact and personal information fall into the wrong hands. Perhaps it already had. How do we really know what will happen to our ID after we give it away? Will our personal information be properly disposed after the contest, or will it be carelessly tossed into the trash, opening the door for identity theft? A sobering question.
Your thoughts on the above case study?
Does this information surprise you?
Stolen Moon Giclee Print - 9 x 12 in.
Buy for $19.99

How To Prevent Your Identity From Being Stolen
Things you can do to keep from being a victim of a crime.
1-Only enter personal information on websites that you trust and it's even better if the security software you're using trusts it as well.
2-Don't throw away trash that has personal information on it without blacking it out, tearing it up into small pieces or using a crosscut shredder on it.
3-Protect your social security number like it was gold and never carry it on you. Never give it out unless absolutely necessary and even then ask if they would accept another number.
4-Be wary of e-mail attachments in any kind of message; make sure you know you can trust the person sending it before clicking on it. This is one way viruses get onto your computer. Thieves can make them look like they come from real companies or government agencies; they can even create convincing copycat sites. Use your contact number if unsure.
5-Make sure your computer and online passwords are not weak. Use a good mix of upper and lowercase letters as well as numbers and symbols. Another good idea would be to keep a copy of your passwords in a separate place in case someone steals your primary list. This way, you'll be able to change them without struggling to recall them.
6-Don't leave mail in your mailbox too early; wait to take it out about an hour or two before your mail is usually picked up. A raised flag alerts your box to thieves as well as the mailman.
7-Try to stay up to date on the latest scams; this information is fairly easy to find on the internet.
8-Always look over credit card and checking account statements carefully to catch any fraud early. You'd be surprised how many people just glance over it.
9-Don't give out personal information over the phone unless you call them. The same thing can be said about e-mail.
10-When paying by credit card, make sure you see the person swipe it. There have been instances where some thieves will swipe your card twice - once legitimately and once to get your information on a separate card reader.
11-Be aware when punching in passwords, make sure no one is watching from over your shoulder. Don't be afraid to cover the keypad with your other hand.
12-Check your credit report at least once a year (2 or 3 is better). You can get a free copy by visiting annualcreditreport.com or calling 1-877-322-8228. These resources were created by way of The Fair Credit Reporting Act requiring Equifax, Experian and TransUnion to provide you with a free copy of your credit report once every 12 months. I usually request reports from one company at a time every 4 months (3 times a year).
13-If you are on the internet at all, make sure you have some kind of security software. Avoid this piece of advice and sooner or later you'll have a bad day.
14-Signing all official documents and checks with your full name (first, middle, last) while using only a first and last name for all other purposes will make things a little more difficult for someone looking to use your good name for their own purposes.
Choose A Crosscut Paper Shredder - For a more complete shredding of documents.
There might actually be someone out there willing to tape together long strips of paper, but not thousands of little squares.
Other Resources To Help With Your Case of Stolen Identity
The sites below go into great detail on identity theft statistics and how to report identity theft. If it ever does happen to you, don't ignore the problem.
- Identity Theft Resource Center
A nonprofit organization that works very closely with governments to prevent and manage cases of stolen identity. Hundreds of articles. - Fighting Back Against Identity Theft
A site run by the Federal Trade Commission of the U.S. government. - Stolen Identity? Here's What to Do
An excellent place to start if you suspect your identity has been stolen.
No Trespassing - January 3, 1942
12 x 16 in. Giclee Print by J.C. Leyendecker
Buy for $39.99
Companies that help with identity theft protection - for a price - A fairly solid way to stop identity theft or at the very least swing the odds in your favor.
- LifeLock
A leading company in identity protection services that seems to always be making improvements to your benefit. - Protect My ID
Another solid company offering protection services. - Identity Guard
A rock-solid choice, even though it costs a little bit more than most.